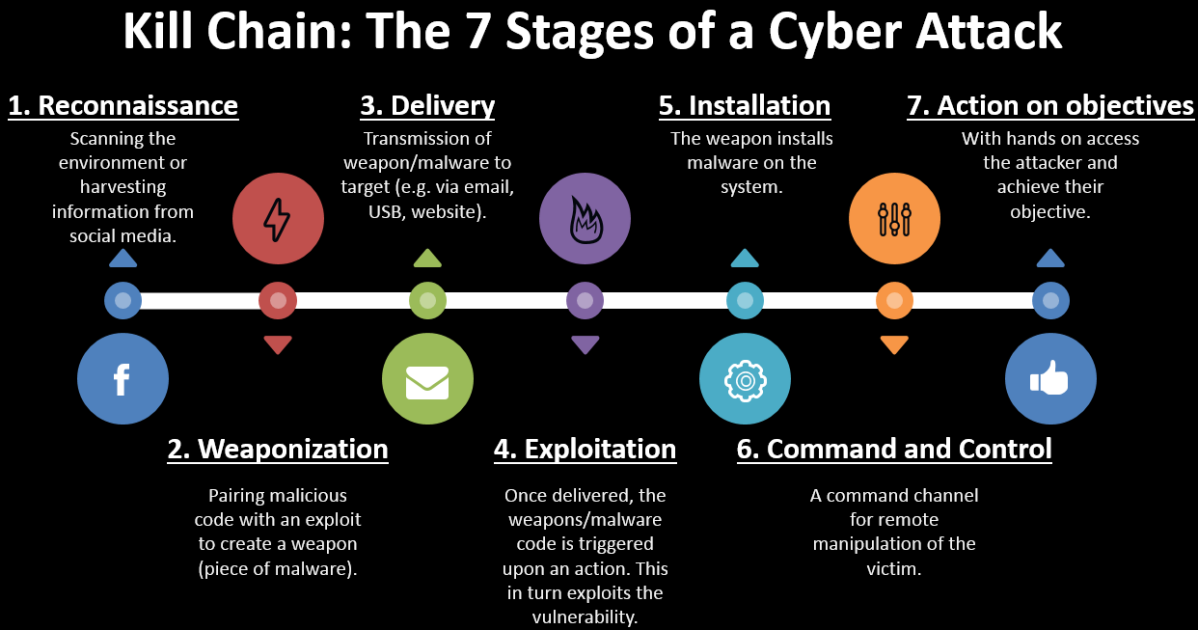
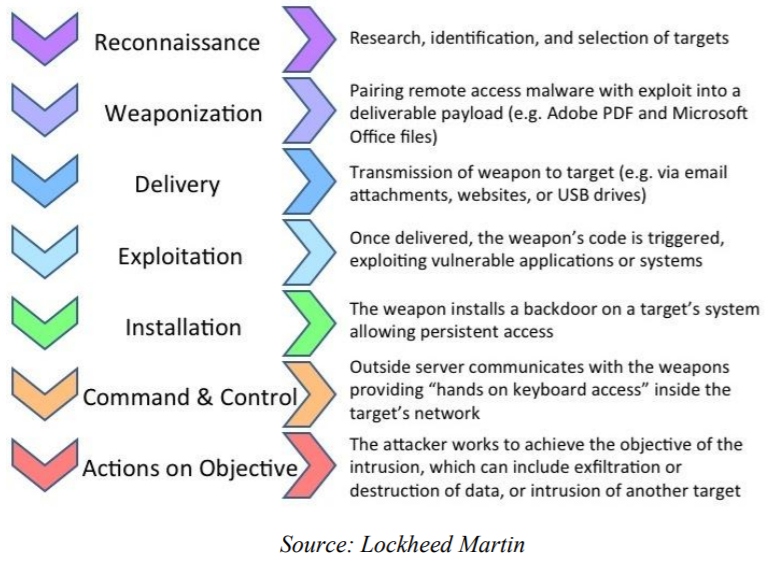
Is the Cyber Kill Chain Model the Ultimate Solution to Rising Ransomware Attacks? - United States Cybersecurity Magazine

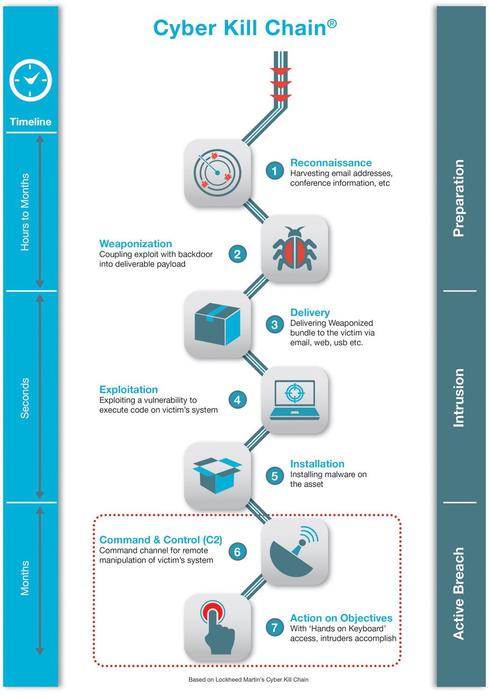
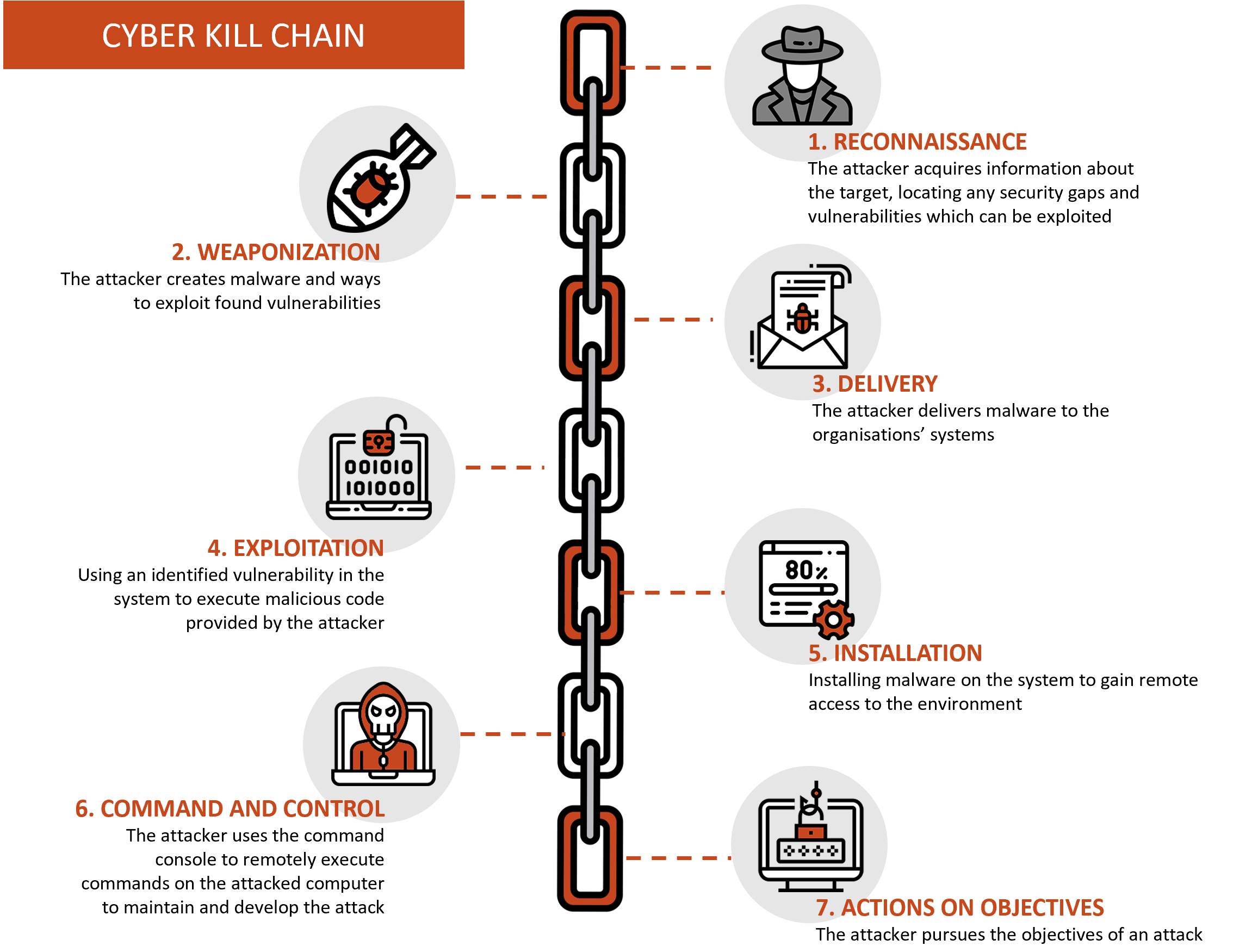
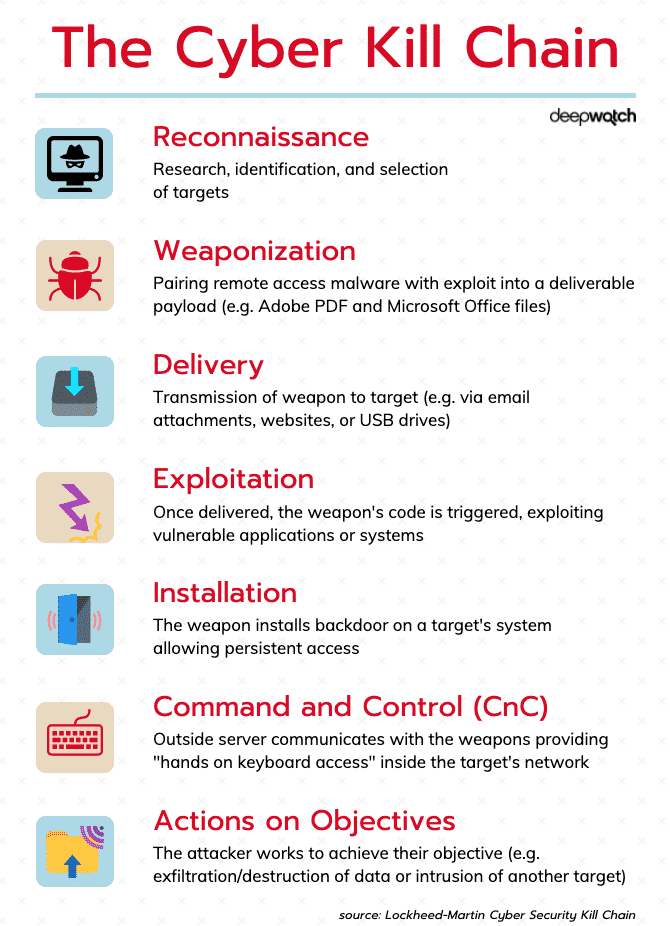
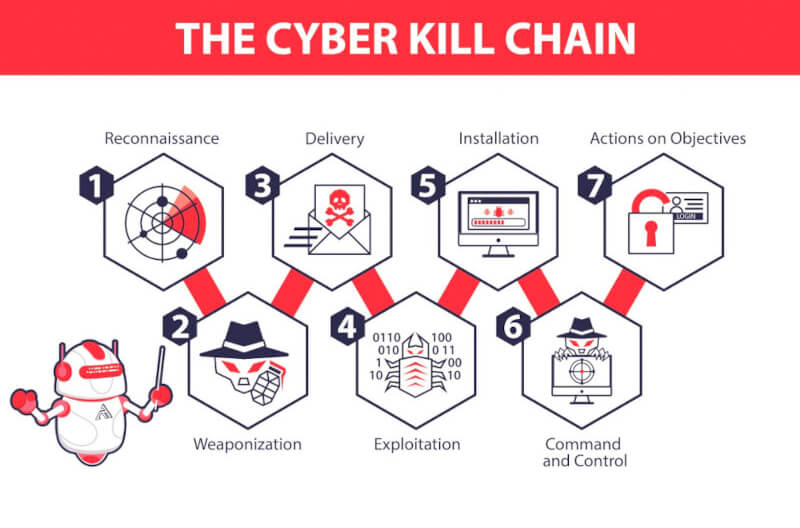
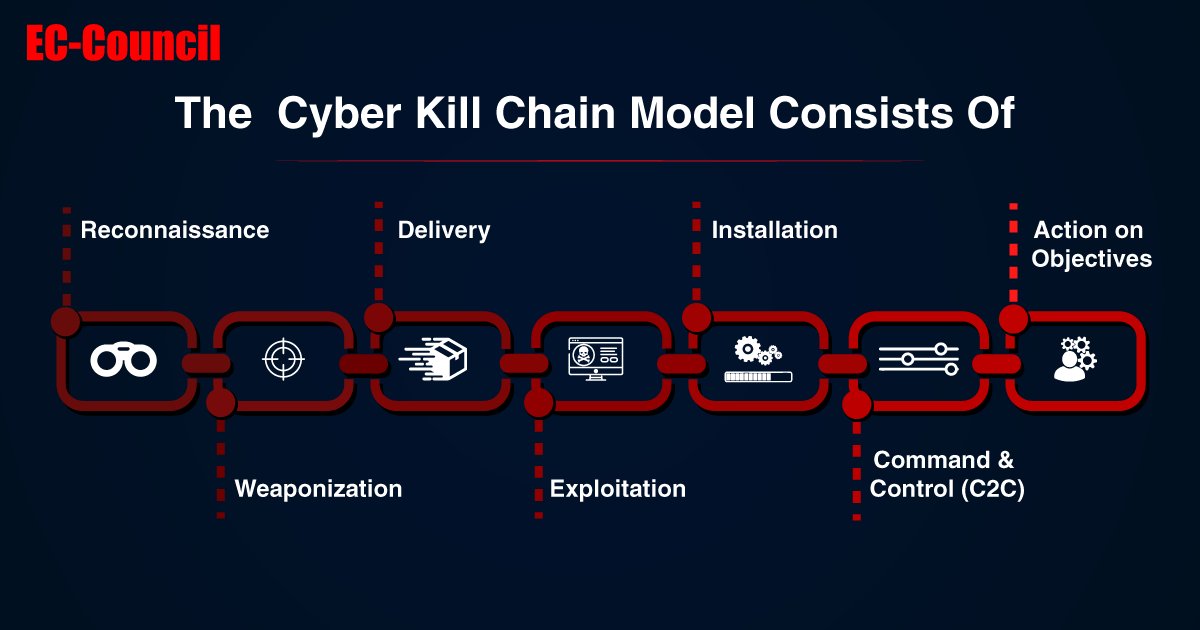
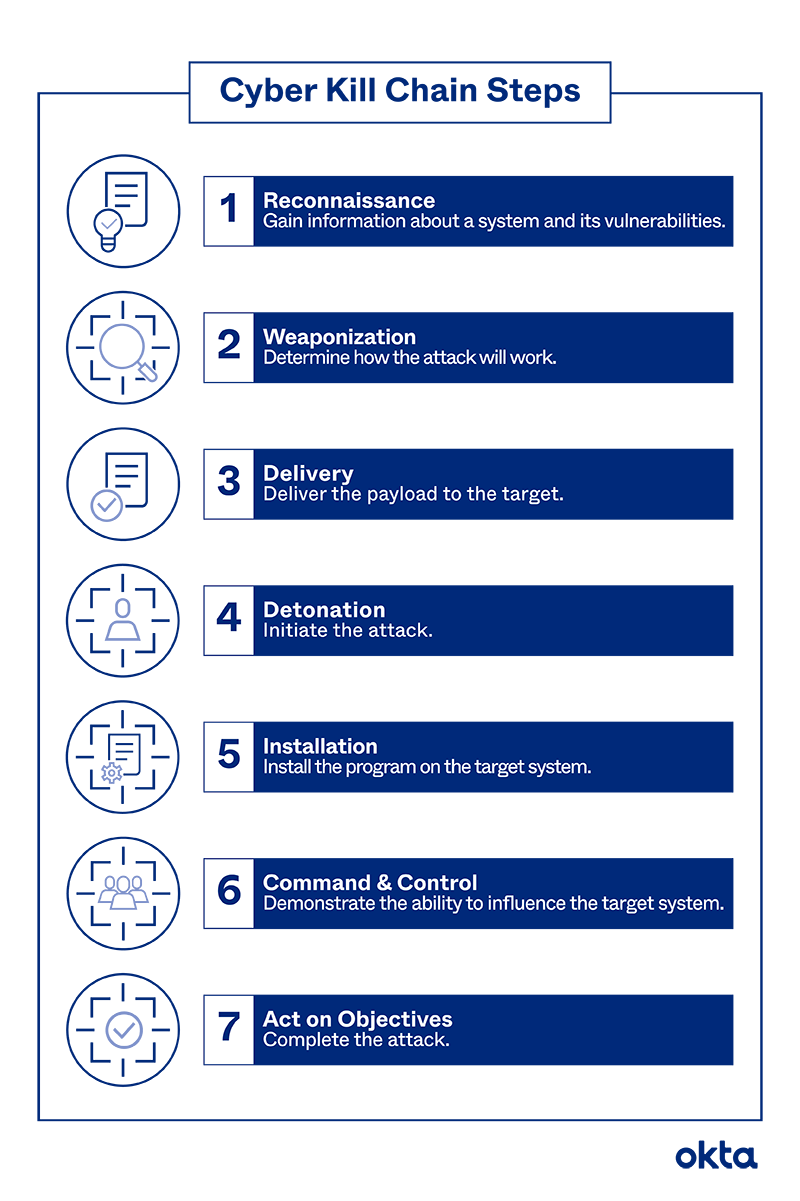
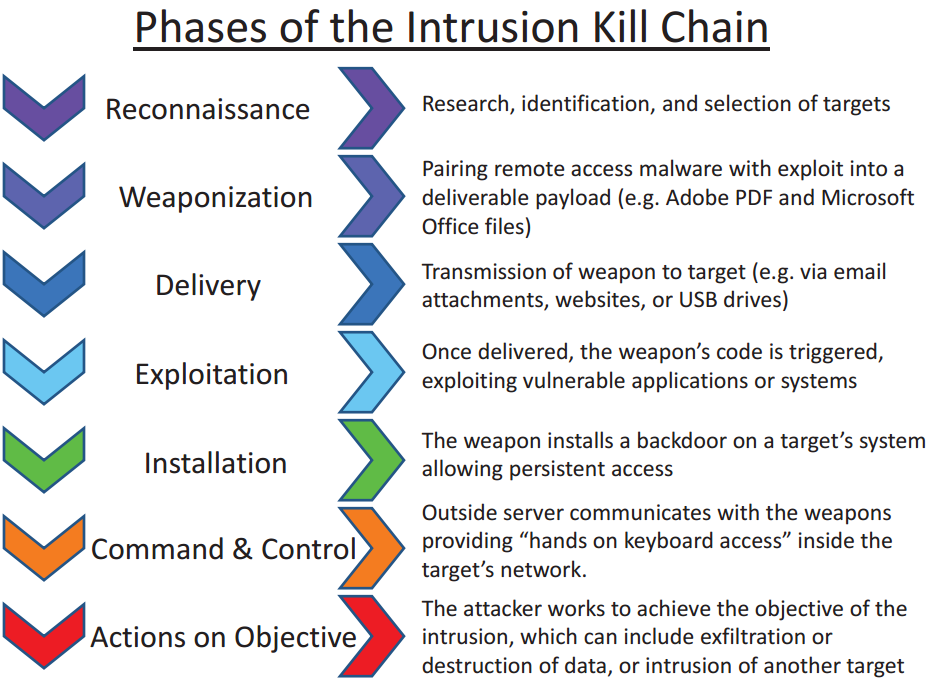
EC-Council - The cyber kill chain helps prepare the organization for all common threats such as network breaches, data thefts, ransomware attacks, and advanced persistent attacks. Let's read more about the cyber




![PDF] The Industrial Control System Cyber Kill Chain | Semantic Scholar PDF] The Industrial Control System Cyber Kill Chain | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/db9041bc1cb494fafec5b04783f3d9623393331a/21-Figure7-1.png)